A series of dangerous security flaws have been discovered in the Ingress NGINX Controller for Kubernetes, putting thousands of clusters at risk. The vulnerabilities enable attackers to execute code remotely without authentication, potentially compromising entire Kubernetes environments.
Security researchers at Wiz identified five critical vulnerabilities, collectively named "IngressNightmare", affecting over 6,500 publicly exposed clusters. The flaws received a severity score of 9.8 out of 10 on the CVSS scale.
Impact and Scope
The vulnerabilities specifically target the admission controller component of Ingress NGINX Controller. Research shows that approximately 43% of cloud environments are vulnerable, including systems belonging to Fortune 500 companies.
When exploited, these flaws allow attackers to:
- Execute arbitrary code remotely
- Access sensitive secrets across all cluster namespaces
- Potentially take complete control of affected clusters
Technical Details
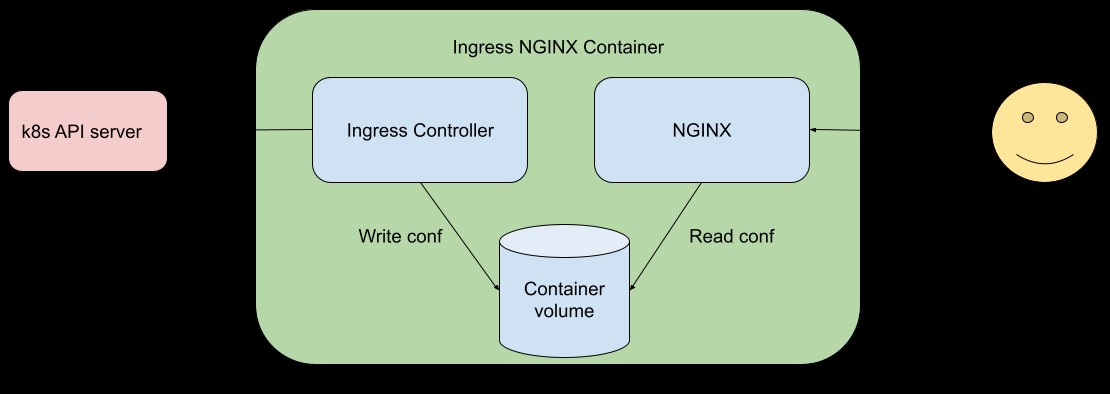
The main vulnerability stems from the admission controller being network-accessible without authentication requirements. Attackers can inject malicious NGINX configurations by sending specially crafted ingress objects to the admission controller.
The five identified vulnerabilities are:
- CVE-2025-24514: auth-url Annotation Injection
- CVE-2025-1097: auth-tls-match-cn Annotation Injection
- CVE-2025-1098: mirror UID Injection
- CVE-2025-1974: NGINX Configuration Code Execution
Mitigation Steps
Organizations using affected versions should:
- Update to patched versions (1.12.1, 1.11.5, or 1.10.7)
- Verify admission webhook endpoints are not publicly exposed
- Restrict admission controller access to only the Kubernetes API Server
- Temporarily disable the admission controller if immediate patching isn't possible
The Kubernetes security team worked closely with researchers to address these vulnerabilities before public disclosure. Users are strongly advised to implement the recommended mitigations as soon as possible to protect their environments.