A sophisticated web skimming operation targeting online merchants has been discovered exploiting an older Stripe API to validate stolen payment card data before theft, security researchers revealed.
According to findings from Jscrambler's research team, attackers are compromising e-commerce websites to inject malicious code that creates fake payment forms mimicking legitimate Stripe checkout pages. The campaign has impacted 49 merchants so far, with 15 sites having removed the malicious code after discovery.
The attack leverages Stripe's deprecated "api.stripe.com/v1/sources" endpoint, which was originally designed to process various payment methods. This allows the attackers to verify card details are valid before exfiltrating the data, making their operation more efficient and stealthy.
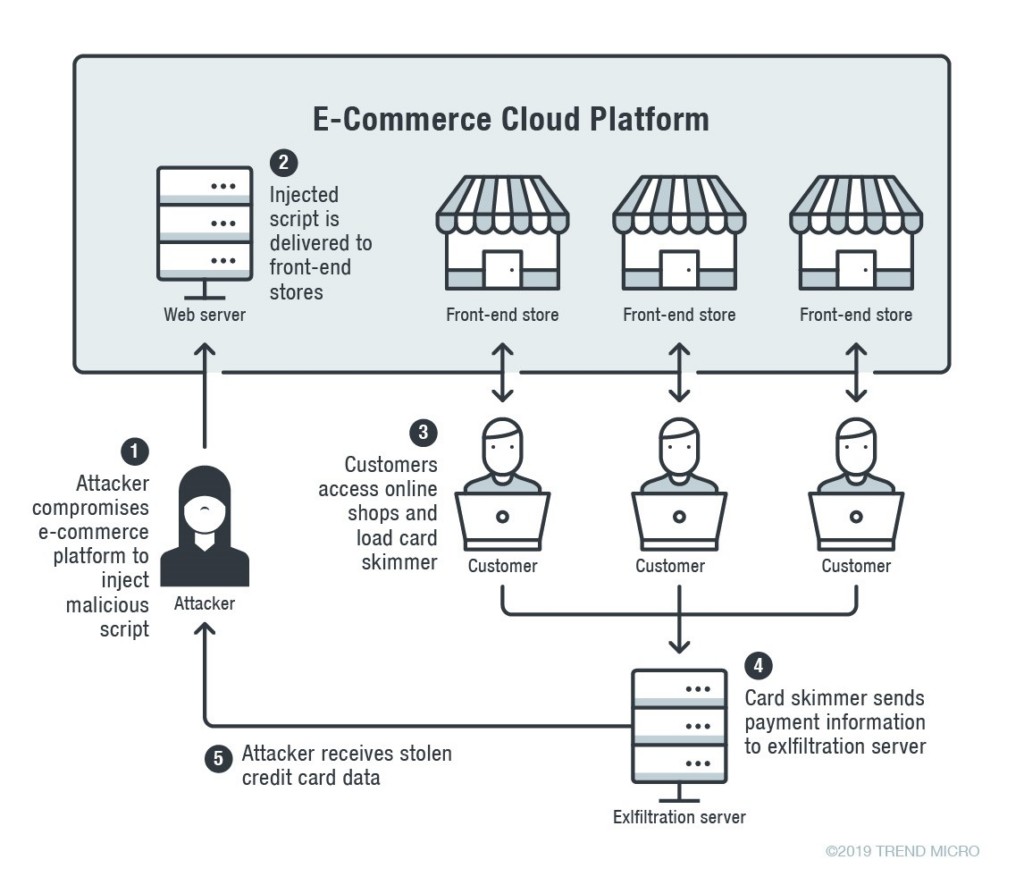
The multi-stage attack begins when threat actors exploit vulnerabilities in popular e-commerce platforms like WooCommerce, WordPress, and PrestaShop to plant malicious JavaScript code. This initial script then loads and decrypts additional code containing the actual payment card skimmer.
When shoppers reach checkout pages, the skimmer hides the legitimate payment form and displays a fraudulent copy. After capturing entered card details, the malware validates them through the Stripe API and sends valid credentials to attacker-controlled servers in encoded format. Users then see an error message prompting them to reload the page.
Researchers noted the skimmer code appears customized for each targeted website, suggesting automated tools may be involved in its generation. Beyond Stripe, evidence shows the attackers are also impersonating Square payment forms and have added cryptocurrency payment options including Bitcoin, Ethereum, Tether and Litecoin.
The campaign has been active since at least August 2024 and continues to pose risks to online merchants and their customers. Security firm Source Defense initially detected the activity in February 2025.
This sophisticated operation demonstrates how cybercriminals continue advancing their tactics to steal payment data while avoiding detection through careful validation of stolen credentials.