A sophisticated backdoor discovered in the xz compression software in March 2024 sent shockwaves through the open source community. The malicious code, covertly inserted over three years by a maintainer using the pseudonym Jia Tan, could have enabled remote code execution on affected Linux systems with SSH installed.
While the backdoor was eventually caught by a Postgres developer at Microsoft, the incident highlighted vulnerabilities in open source supply chains. However, the NixOS Linux distribution's approach to reproducible builds could have detected this threat earlier.
How the Backdoor Worked
The attack relied on two key components:
- A script that installed a malicious object file during xz builds, but only when using official release tarballs
- Code that hijacked SSH's RSA decryption function to enable remote access
The backdoor specifically targeted Linux distributions where SSH was linked to systemd, which in turn depended on the compromised xz library.
NixOS's Defense Potential
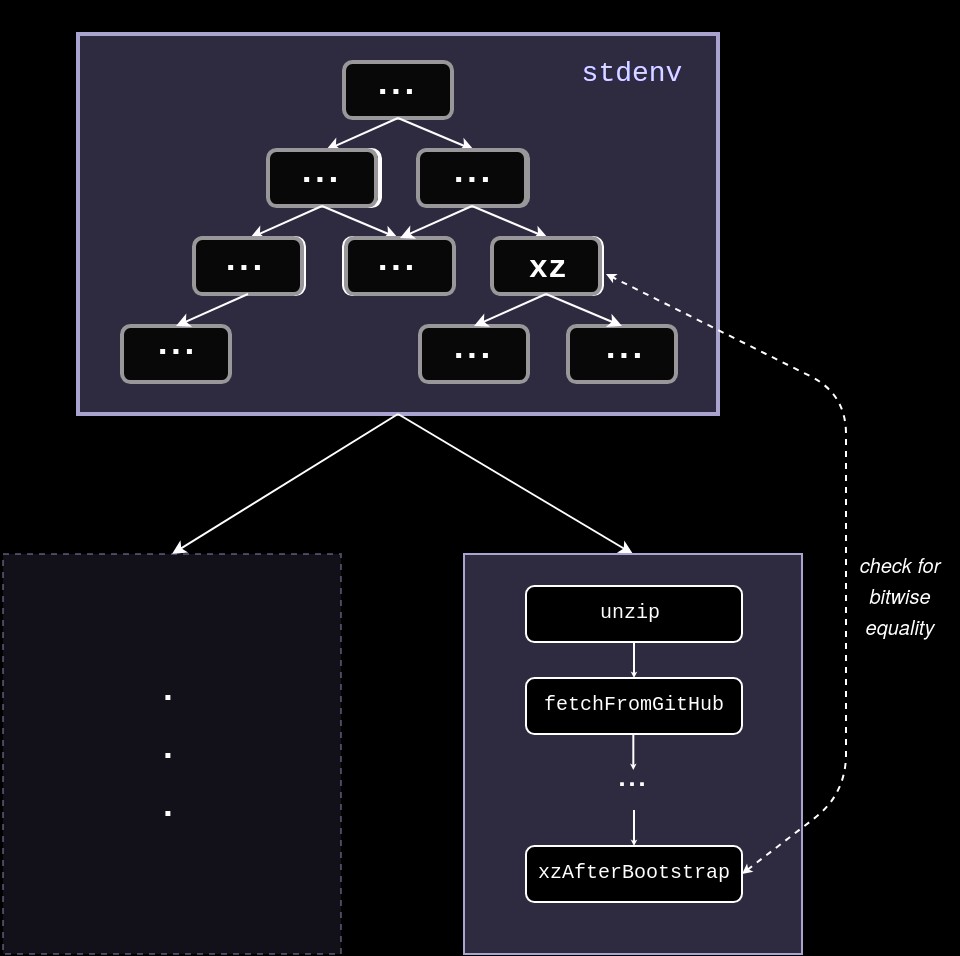
NixOS builds packages using a functional approach where each build process is precisely specified. While NixOS was affected by the backdoored xz version, its architecture enables a powerful verification method:
- Build xz twice - once using the maintainer's tarball during bootstrap, and again later using GitHub source code
- Compare the resulting binaries for discrepancies
- Flag any differences as potential supply chain compromises
When tested against the backdoored xz version, this approach successfully detected added malicious code by revealing suspicious new functions.
Looking Forward
The incident demonstrates the need for more robust software supply chain security. Key recommendations include:
- Building software directly from trusted source code repositories rather than maintainer tarballs where possible
- Implementing reproducible builds to verify package integrity
- Adding automated binary comparison checks for critical bootstrap packages
While not a complete solution, reproducible builds provide an important tool for detecting supply chain attacks. The NixOS community is working to expand these protections across its package ecosystem.
The xz backdoor serves as a wake-up call for improving open source security. NixOS's reproducible build system offers a promising model for strengthening software supply chain defenses industry-wide.