Critical Zero-Day Vulnerability in Chrome Targets Russian Institutions
A sophisticated zero-day vulnerability in Google Chrome allowed attackers to bypass sandbox protection through targeted phishing campaigns against Russian organizations. The recently patched CVE-2025-2783 flaw enabled automatic infections through malicious forum invitation links.
CIA Embraces Signal: Agency Director Reveals Encrypted Messaging App Pre-installed on Official Computers
CIA Director John Ratcliffe disclosed that Signal, an end-to-end encrypted messaging app, comes pre-installed on CIA computers for official communications. The revelation comes amid controversy over sensitive military discussions conducted through Signal, sparking debate about security protocols in government communications.
Signal's Privacy Dominance: A Deep Dive into the World's Most Secure Messaging App
Signal's end-to-end encryption and privacy-focused features have made it the top choice for secure messaging, attracting millions of users from journalists to government officials. Recent incidents involving Trump administration officials highlight both Signal's effectiveness and the challenges of balancing security with proper communication protocols.
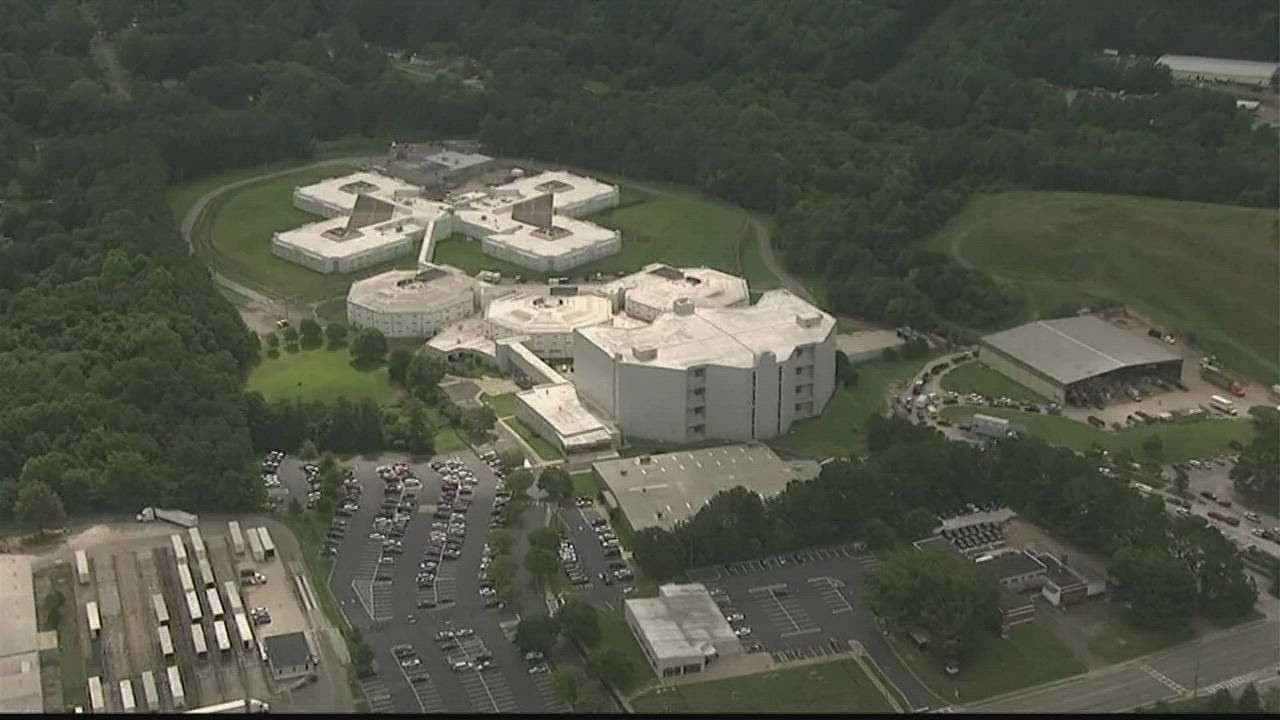
Georgia County Downplays Suspicious Server Activity Amid Service Disruptions
Cobb County officials remain vague about a potential cybersecurity incident that forced multiple servers offline, initially framing it as routine maintenance. The situation has affected various online services and raised questions about transparency in handling digital threats.
The Race Against Q-Day: How Quantum Computing Threatens Global Digital Security
A quantum computing breakthrough could soon shatter modern encryption, threatening global digital infrastructure from power grids to cryptocurrencies. Experts warn there's a one-in-three chance this 'quantum apocalypse' arrives before 2035, sparking an urgent race to implement quantum-resistant security.
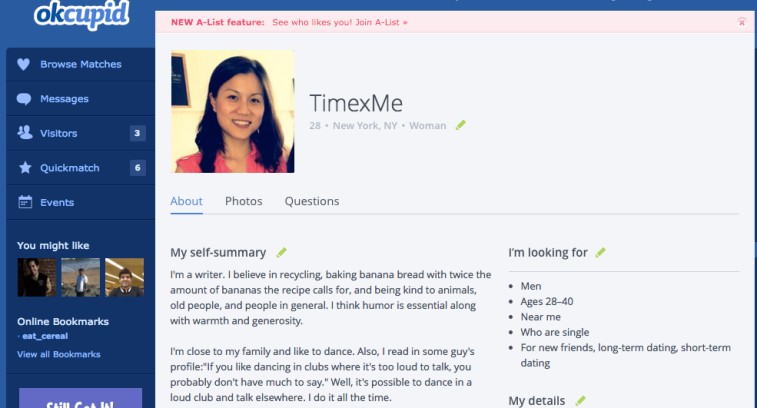
Dating App's Email Security Flaws Expose User Privacy Concerns
OkCupid's flawed email validation practices have led to unauthorized account creations and privacy breaches, with users receiving notifications for accounts they never created. The dating platform's inadequate response raises serious questions about their security measures and commitment to user privacy.
Kali Linux 2025.1a Brings Major Overhaul with Enhanced Mobile Hacking Features
The latest Kali Linux release delivers a complete visual refresh with KDE Plasma 6.2 and Xfce 4.20 upgrades, plus significant improvements to its NetHunter mobile platform. The update also brings full Raspberry Pi 5 support and expanded car hacking capabilities.
Chinese E-Commerce Sites Selling Dangerous Drone Modifications That Could Transform Toys Into Weapons
Security researchers uncover alarming trend of Chinese platforms selling low-cost drone accessories capable of weaponizing commercial quadcopters. The components, mirroring technology used in warfare, include AI guidance systems and signal-jamming countermeasures available for just hundreds of dollars.
Major Stalkerware Data Breach Exposes 2 Million Users, Including Apple iCloud Credentials
A significant data breach at SpyX surveillance software has compromised nearly 2 million user records, including 17,000 Apple iCloud credentials. The incident highlights growing concerns around consumer spyware misuse and inadequate breach disclosure practices in the surveillance industry.
Google's Record $32B Acquisition of Wiz Reshapes Cloud Security Landscape
Google's parent company Alphabet makes its largest-ever acquisition, purchasing cybersecurity startup Wiz for $32 billion. The strategic move aims to bolster Google Cloud's security capabilities while maintaining Wiz's cross-platform services.