Firefox Privacy Crisis: How to Protect Your Data in Mozilla's New Era
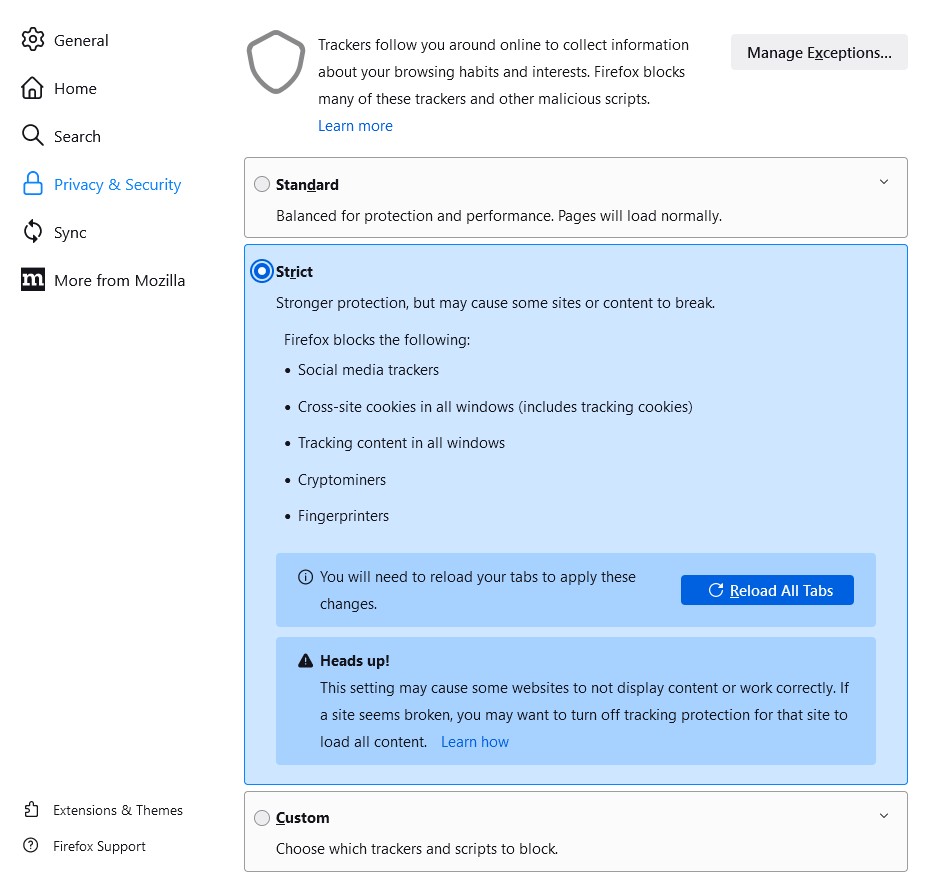
Mozilla's latest privacy policy changes grant broader control over user data, marking a departure from Firefox's privacy-first legacy. Learn essential steps to safeguard your privacy while using the browser, from enhanced settings to alternative options.
Self-Hosted Firefox Sync: A Guide to Reclaiming Your Browser Data Privacy
Learn how privacy-conscious Firefox users are taking control of their browsing data by setting up personal sync servers. This comprehensive guide explores the benefits and technical requirements of self-hosting Firefox Sync using modern Rust-based solutions.
Mozilla's Privacy Terms Update Sparks User Concerns Over Data Rights
Mozilla's revised Firefox Terms of Use has triggered widespread debate over user privacy implications, requiring a broad license for browser functionality. The organization maintains the changes are necessary for basic operations, though some users remain skeptical of the expanded terms.
Mozilla Introduces First Privacy Terms for Firefox, Marking New Era in Browser Transparency
Mozilla is implementing its first-ever Terms of Use for Firefox, along with an updated Privacy Notice, prioritizing user privacy and control. The landmark change requires new users to acknowledge terms starting March, while existing users will see changes later this year.
John Oliver's Privacy Guide Takes Aim at Meta's Data Collection Empire
Last Week Tonight host John Oliver launches a partnership with EFF to help users protect their personal data from Meta's tracking practices. The initiative includes practical privacy tools and browser recommendations to limit the tech giant's ability to monetize user information.
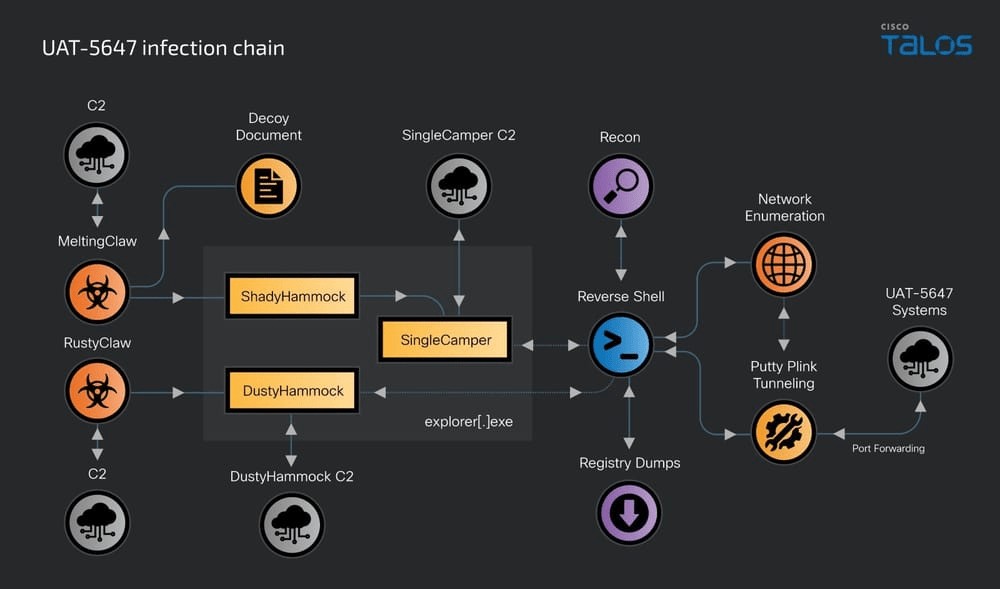
Zero-Click Attack: RomCom Hackers Exploit Firefox and Windows Flaws
Russian hacking group RomCom orchestrated a sophisticated cyber attack by exploiting zero-day vulnerabilities in Firefox and Windows Task Scheduler, requiring no user interaction. The campaign targeted organizations across Europe and North America, highlighting the growing capabilities of state-aligned threat actors.